A Deep Dive into Saudi Arabia's Cybersecurity Landscape
Introduction
We see millions of cybersecurity threats identified each day, but not all of these are zero-day assaults. In truth, zero-day assaults account for 0.1% to 2% of the total, whereas the remaining assaults target existing vulnerabilities. This implies these vulnerabilities are as of now showing and encompassing us, posing a persistent risk to our digital security. In this web journal, we will investigate the leading nation in the Middle East that is taking critical cybersecurity awareness measures to improve assurance against cyberattacks.
Kingdom of Saudi Arabia's Cybersecurity Evolution
Saudi Arabia is the territorial cyber pioneer in the Middle East and has been truly contributing to both network security and ability improvement. It has taken several steps over a long time to mitigate and avoid cybersecurity threats. Following is how the country advanced its cyber strategy:
Early 2000s: Initial Awareness and Infrastructure Development: In the early twenties, Saudi Arabia started understanding the importance of cybersecurity for small business protection. The country mainly focused on developing a foundation framework and raising cybersecurity awareness about almost all cyber threats. This period tested the foundation of starting cybersecurity systems and offices aimed at ensuring computerized resources.
2007-2010: Emerging Cyber Risks: Moreover, this was the spell when cyberattacks on Saudi Arabia started to escalate, and more of them were suddenly popping up everywhere. This new trend created a necessity for even more reliable computer security. Consequently, Saudi Arabia was actively looking for innovative security technologies, and even those that were available had additional defense mechanisms to counteract novel risks.
2011-2015: Reforms of Cybersecurity Policy: Saudi Arabia has taken a step into the formalization realm of cybersecurity and infrastructure security agency policies and regulations to be in line with the latest technology standards. One such strategy is the National Cybersecurity Program that allows for the development of standards and their enforcement. These measures bring flexibility and scalability to cyber-resilience.
2016-2020: Expansion and Modernization: This phase focused on the huge expansion and modernization of network security measures. The kingdom largely supported cybersecurity companies and investment in technology, introduced new cybersecurity tools, and increased partnerships with other countries to improve defense capabilities.
2021-Present: Enhanced Focus and Global Integration: Saudi Arabia has placed significant emphasis on Cybersecurity Awareness Month, adopting advanced technologies and modern strategies. Global cybersecurity collaborations have strengthened monitoring, response, and regulatory capabilities—demonstrating commitment to preventing and mitigating cybersecurity threats.
SAUDI ARABIA'S CYBER SECURITY STRATEGIES
Saudi Arabia actively pushes the cybersecurity for small business framework to safeguard primary sensitive digital assets and infrastructure.
National Cybersecurity Authority (NCA): The NCA, established in 2017, is tasked with regulating and enforcing crucial national network security policies. It also provides strategic advice to public and private entities to ensure adherence to security standards.
Regulatory Frameworks and Cybersecurity Policies: Saudi Arabia prepared a national cybersecurity blueprint that protects the administration, private companies, and finance systems against cybersecurity threats. Key laws include the Essential Cybersecurity Controls (ECC-1) to ensure compliance in secure data transmission, finance, energy, and telecommunication.
Cybersecurity Talent Development: The CyberIC program trains not fewer than 40,000 individuals in the cybersecurity field for small businesses by 2030. Training programs and certification are provided by educational institutions and global cybersecurity companies.
Investment in Emerging Technologies: The government invests in AI, machine learning, big data, and blockchain to improve computer security, threat detection, and predictive cybersecurity analytics.
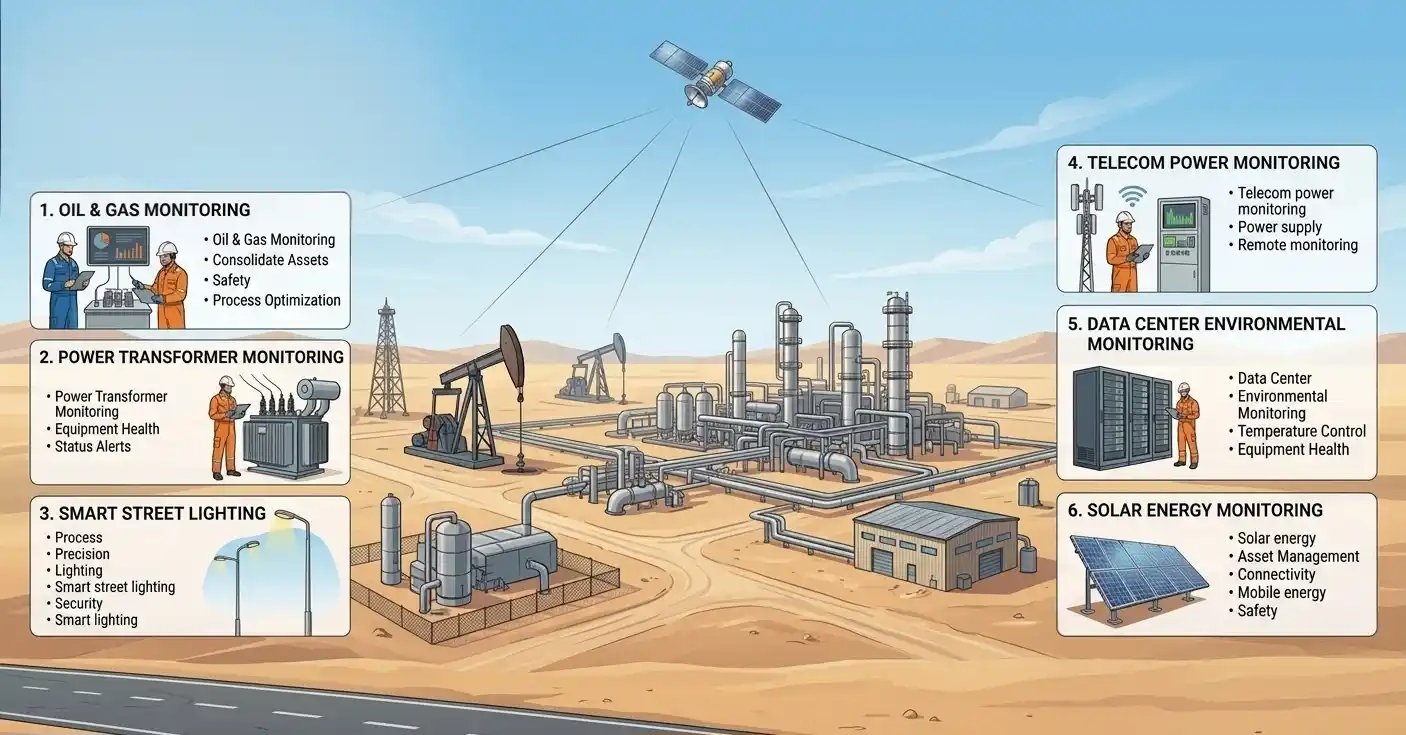
Critical Infrastructure Protection (CIP): Specialized cybersecurity strategies protect critical sectors like oil, gas, electricity, and water. Public-private partnerships ensure secure operations and resilience.
Public-Private Partnerships (PPP): Collaborations aim to implement secure cybersecurity operations and technological security systems.
International Collaboration: Saudi Arabia participates in global cybersecurity discussions, with support from INTERPOL, the UN, and GFCE, enhancing cybersecurity awareness globally.
Cybersecurity Awareness Campaigns: Campaigns educate citizens and employees on cyber hygiene and protection from phishing, social engineering, and malware exploits.
Cyber Incident Response and Recovery: Cyber incidents are detected and mitigated rapidly, leveraging AI tools and the National CERT (Computer Emergency Response Team).
Cybersecurity as a National Priority: Cybersecurity is a priority in Saudi Vision 2030. By focusing on cybersecurity awareness, the government strengthens resilience to both internal and external threats.
Real-World Example: The Shamoon Virus Attack
In 2012, the Shamoon virus attacked Saudi Aramco, affecting 30,000 computers and disrupting operations. This incident led to updates in cybersecurity strategies and improvements in cybersecurity for small businesses and critical infrastructure protection.
Conclusion
Saudi Arabia's journey in cybersecurity demonstrates a strong commitment to cybersecurity awareness, advanced network security, talent development, investment in emerging technologies, and collaboration with global cybersecurity companies. These efforts have reinforced the country's digital landscape and strengthened protection against cybersecurity threats.
Let's Connect and Protect Together!
No organization is too small to become a target today. As I have shown along the line in this blog, cybersecurity awareness is not a need but an investment in the future of your organization. If you are interested in protecting your organization or just want to swap knowledge on the latest in cybersecurity, let's connect! You can reach out to me on LinkedIn at any time, and together we can help each other build a safer digital future!